Process Description
This page describes the complex onboarding process used for Customer Onboarding and Mobile App Registration flows.
Wultra implements the critical process of onboarding, which is provided on the mobile platform by Wultra’s SDK:
- SDK will be integrated into the existing providers application and provide onboarding and Strong Customer Authentication (SCA) on the device. The whole onboarding process is designed as a mobile only
It’s important to note that the process boosts security by:
- Adding a step that cannot be phished out easily - while the user can pass it easily, there’s no information the user gives away to the attacker
- Capturing the photo of a person using the device on which the registration takes place (which is, on its own, a protective measure)
The digital onboarding process consists of a set of checks and validations in a flow designed to maximize the conversion rate while keeping up with regulatory (KYC and AML) and internal security requirements
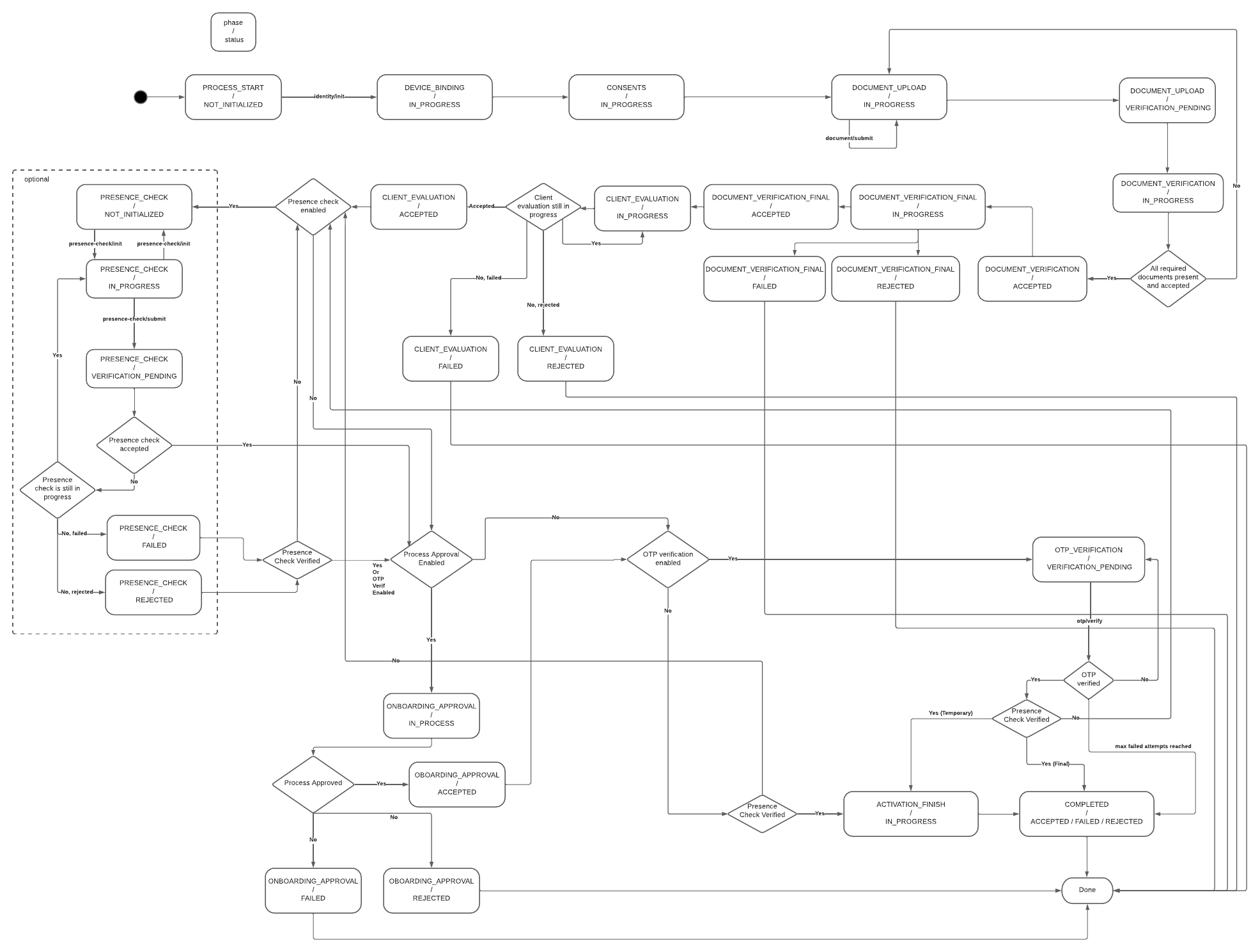
Process Diagram
The diagram below illustrates all the steps in the process. The core functionalities are document OCR with verification and liveness checks (server-side biometrics), and we provide additional optional functions such as consent or one-time passwords.
The system calls services that should be implemented by the client. Most of these services are optional, except for the User Lookup Service, which returns a User ID to enable the client to establish a connection between the onboarding process and their own user database.
The user journey can be amended and will be finalized during the analysis phase.
State Diagram
Activating a new mobile application (e.g., an existing customer with a new phone) uses the same core components of ID scanning and verification and liveness detection. In this scenario, the components are combined to check an existent identity and are typically combined with SMS OTP.
It’s important to note that Digital Onboarding boosts security by:
- Adding a step that cannot be phished out easily - while the user can pass it easily, there’s no information the user gives away to the attacker.
- Capturing the photo of a person using the device on which the registration takes place (which is, on its own, a protective measure).
Mobile App Activation Flow
The KYC process itself is driven by a mobile-facing component called the Onboarding Server. This ensures that the mobile application (represented by the Onboarding SDK) is informed of the current and next steps in the process, enabling it to display the appropriate screen.
For simplicity, the KYC itself is split on the mobile phone to follow subsequent phases.
- Initial Identification
- Document Verification
- Presence Verification
- Final Verification
In the Initial Identification phase, the Onboarding Server gets the configuration from the KYC Process Server:
- Way to initially identify a user (OTP verification, username, technical identifier)
- List of consents to display for the user
- Which documents should be gathered in the process
- Optional additional OTP verification after the end of the verification process
- Checks and controls (number of allowed failed attempts, daily total attempts per user, etc.)
In Document Verification, the mobile app gathers the required documents per process type configuration and uploads the document scan to the Onboarding Server. The Onboarding Server checks the document with the Cloud API and uploads the result and extracted data to the Client Evaluation Service. After the signal from the KYC processing to approve (or reject) the attempt is received, the process continues.
In the Presence Verification phase, a similar logic applies to face verification. Onboarding Server initiates the verification session with Liveness Check SDK, informs the mobile application, and, after the face is scanned in the mobile application, verifies the result with the Cloud API. After that, inform the Onboarding Approval Service about the result and wait for approval.
After approval, if configured, the SCA signature from the client verifies the remote transaction of the digital onboarding and client.
Onboarding Stages
| Stage | Description |
|---|---|
| User Identification | The user identification flow collects basic user and AML/KYC data, retrieves the required configuration, and starts a new process using user credentials. A semi-optional lookup can validate the user and determine consent needs. If OTP verification is required, it’s sent and entered to create the registration. The user then completes registration by setting a PIN. |
| Identity Verification | The identity verification flow collects user consent, verifies documents, and optionally evaluates client data. Presence and biometric checks are performed, followed by optional onboarding approval. An OTP may be sent for strong customer authentication if required. |
| Device Registration | Device registration differs by type: flagged registrations simply remove the verification flag, while temporary registrations finalize the user ID, create a new registration, and complete PIN/biometric setup. Both types can optionally trigger a process event. The flow concludes with the success screen. |

